QUESTION IMAGE
Question
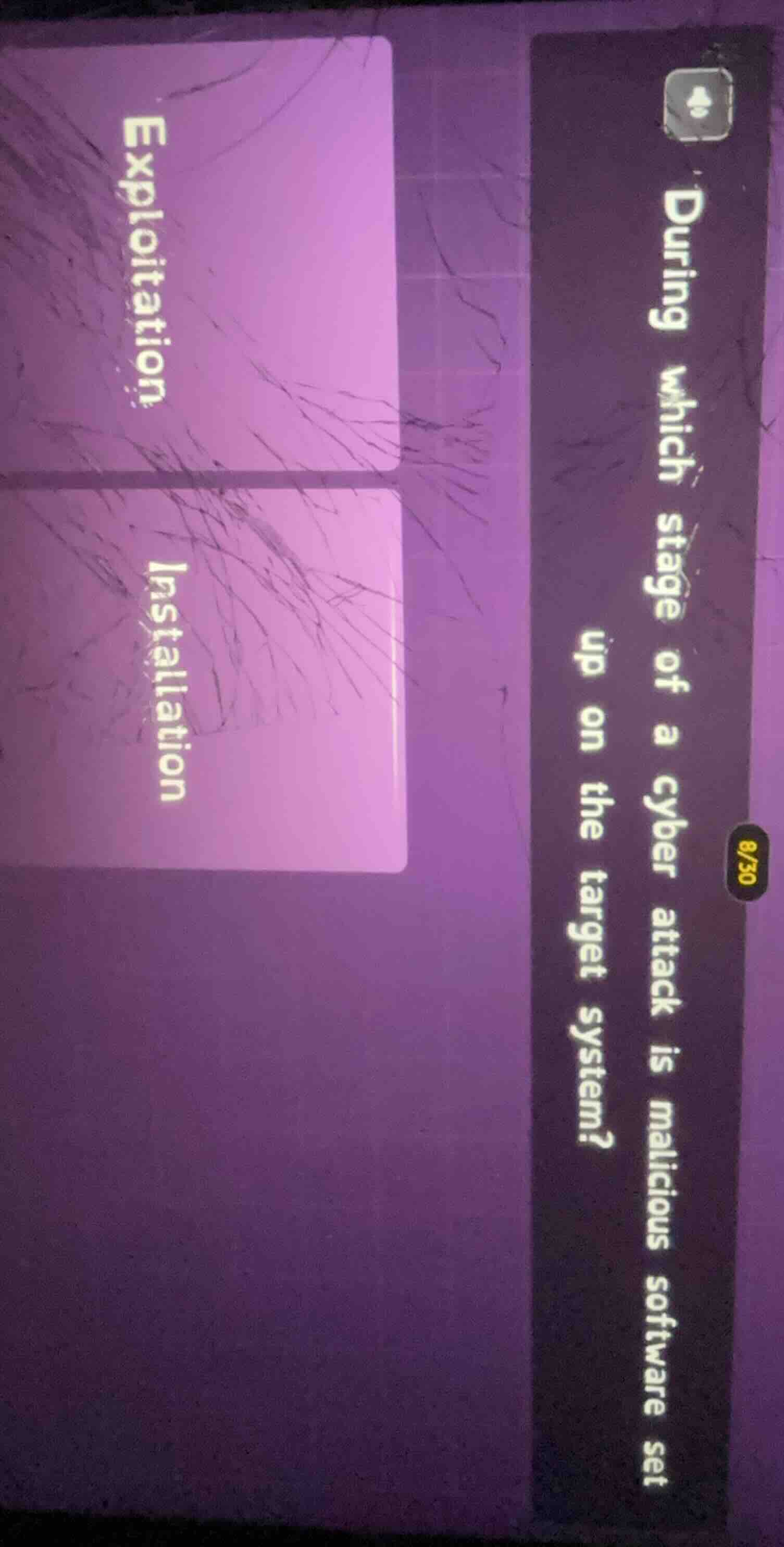
during which stage of a cyber attack is malicious software set up on the target system?
exploitation
installation
In the cyber attack kill chain (or stages of a cyber attack), after exploitation (where vulnerabilities are leveraged to gain access), the next stage often involves installing malicious software on the target system. The "Installation" stage is when the attacker deploys the malicious payload (like malware) onto the compromised system to maintain access or carry out further malicious actions. Exploitation is about gaining access by exploiting a vulnerability, while installation is about putting the malicious software in place on the target system. So the stage where malicious software is set up on the target system is Installation.
Snap & solve any problem in the app
Get step-by-step solutions on Sovi AI
Photo-based solutions with guided steps
Explore more problems and detailed explanations
Installation