QUESTION IMAGE
Question
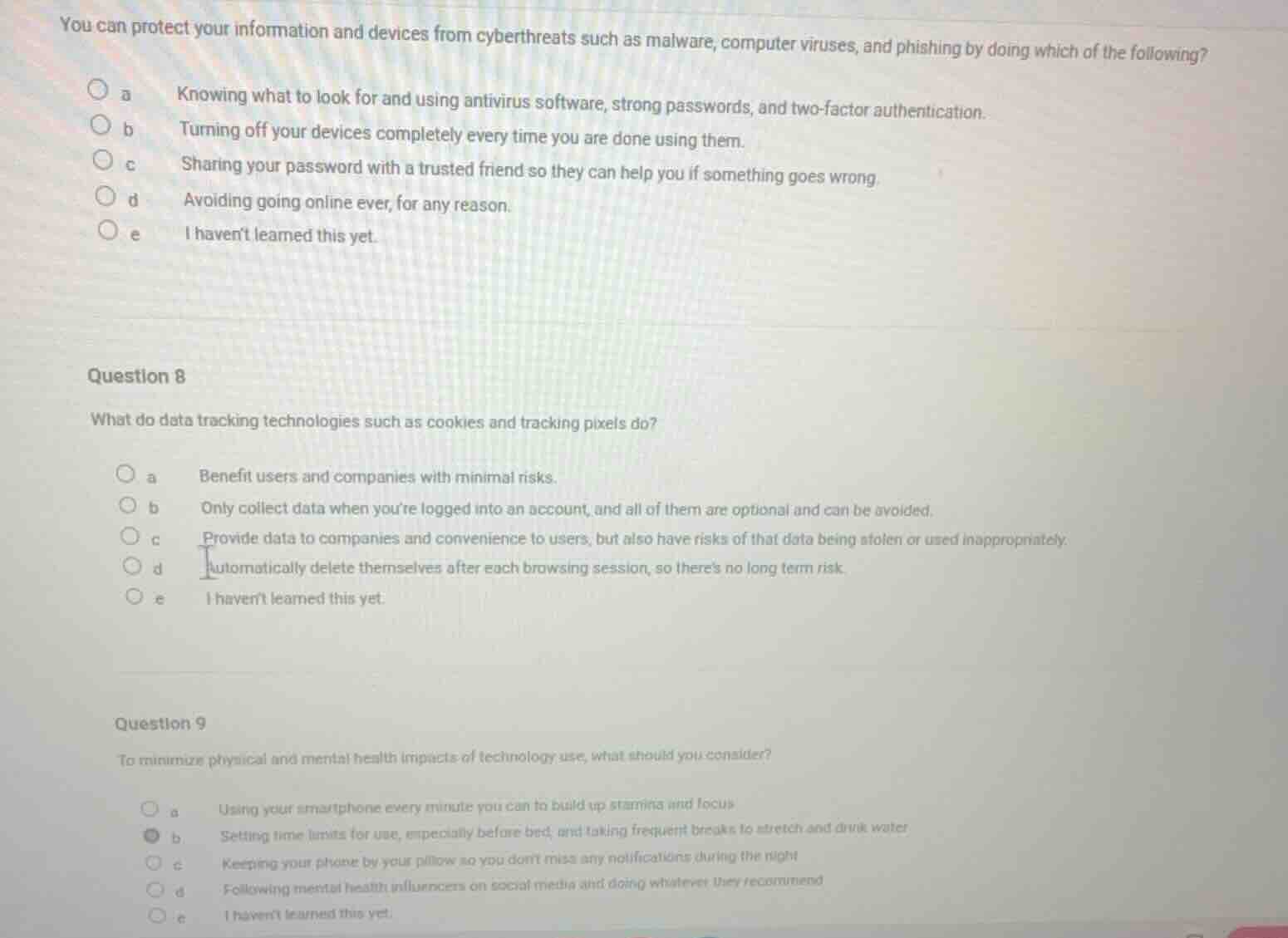
you can protect your information and devices from cyberthreats such as malware, computer viruses, and phishing by doing which of the following?
a knowing what to look for and using antivirus software, strong passwords, and two - factor authentication.
b turning off your devices completely every time you are done using them.
c sharing your password with a trusted friend so they can help you if something goes wrong.
d avoiding going online ever, for any reason.
e i havent learned this yet.
question 8
what do data tracking technologies such as cookies and tracking pixels do?
a benefit users and companies with minimal risks.
b only collect data when youre logged into an account, and all of them are optional and can be avoided.
c provide data to companies and convenience to users, but also have risks of that data being stolen or used inappropriately.
d automatically delete themselves after each browsing session, so theres no long term risk.
e i havent learned this yet.
question 9
to minimize physical and mental health impacts of technology use, what should you consider?
a using your smartphone every minute you can to build up stamina and focus
b setting time limits for use, especially before bed, and taking frequent breaks to stretch and drink water
c keeping your phone by your pillow so you dont miss any notifications during the night
d following mental health influencers on social media and doing whatever they recommend
e i havent learned this yet.
First Question (Cyberthreat Protection)
- Option a: Using antivirus, strong passwords, and 2FA, plus knowing threats, is standard cyber protection.
- Option b: Turning off devices fully isn’t a primary cyberthreat protection method (e.g., malware can still be present if infected).
- Option c: Sharing passwords is a security risk, not a protection method.
- Option d: Avoiding the internet entirely is impractical and not a standard protection approach.
- Option e: Incorrect as the knowledge is standard in digital literacy.
- Option a: Cookies/pixels have risks (e.g., data misuse), so “minimal risks” is incorrect.
- Option b: They collect data even without logging in, and not all are optional/avoidable easily.
- Option c: They provide convenience (e.g., personalized ads) and data to companies but carry risks like data theft/misuse.
- Option d: Cookies (e.g., persistent cookies) don’t always delete after sessions, so long - term risks exist.
- Option e: Incorrect as this is a standard topic in digital literacy.
- Option a: Excessive smartphone use harms health, not “build stamina/focus”.
- Option b: Setting time limits (especially before bed) and taking breaks (stretching, drinking water) reduces physical (eye strain, posture issues) and mental (sleep disruption, stress) health impacts.
- Option c: Keeping phone by pillow disrupts sleep (blue light, notifications), harming health.
- Option d: Blindly following influencers’ advice is risky and not a reliable health - mitigation method.
- Option e: Incorrect as this is a standard health - tech balance practice.
Snap & solve any problem in the app
Get step-by-step solutions on Sovi AI
Photo-based solutions with guided steps
Explore more problems and detailed explanations
a. Knowing what to look for and using antivirus software, strong passwords, and two - factor authentication.