QUESTION IMAGE
Question
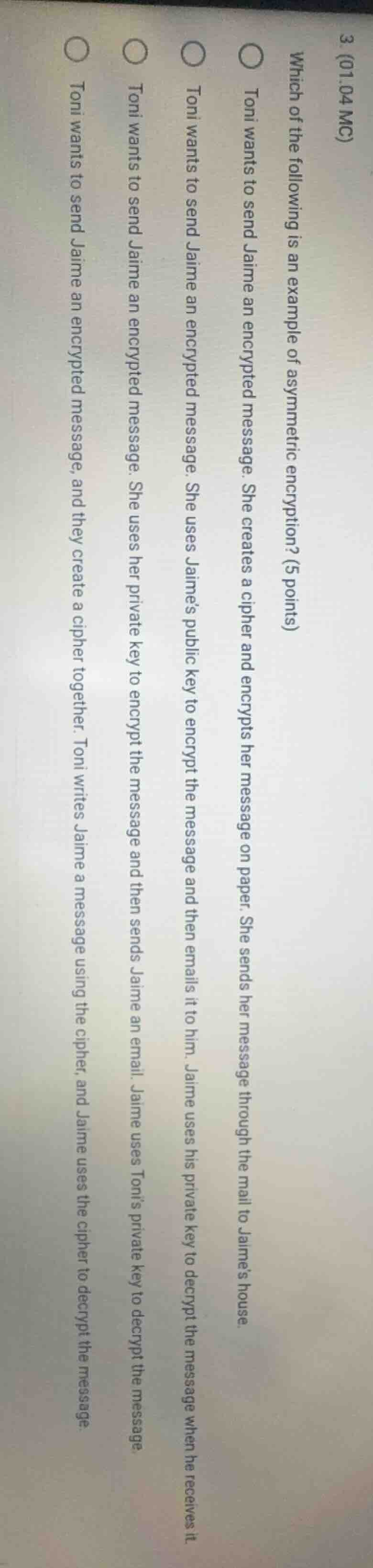
- (01.04 mc)
which of the following is an example of asymmetric encryption? (5 points)
○ toni wants to send jaime an encrypted message. she creates a cipher and encrypts her message on paper. she sends her message through the mail to jaime’s house.
○ toni wants to send jaime an encrypted message. she uses jaime’s public key to encrypt the message and then emails it to him. jaime uses his private key to decrypt the message when he receives it.
○ toni wants to send jaime an encrypted message. she uses her private key to encrypt the message and then sends jaime an email. jaime uses toni’s private key to decrypt the message.
○ toni wants to send jaime an encrypted message, and they create a cipher together. toni writes jaime a message using the cipher, and jaime uses the cipher to decrypt the message.
Asymmetric encryption uses a paired public/private key system: senders encrypt with the recipient's public key, and only the recipient's private key can decrypt the message. The other options use shared ciphers (symmetric) or incorrect key usage (sender's private key for encryption, which is for authentication, not secure message sending).
Snap & solve any problem in the app
Get step-by-step solutions on Sovi AI
Photo-based solutions with guided steps
Explore more problems and detailed explanations
C. Toni wants to send Jaime an encrypted message. She uses Jaime's public key to encrypt the message and then emails it to him. Jaime uses his private key to decrypt the message when he receives it.