QUESTION IMAGE
Question
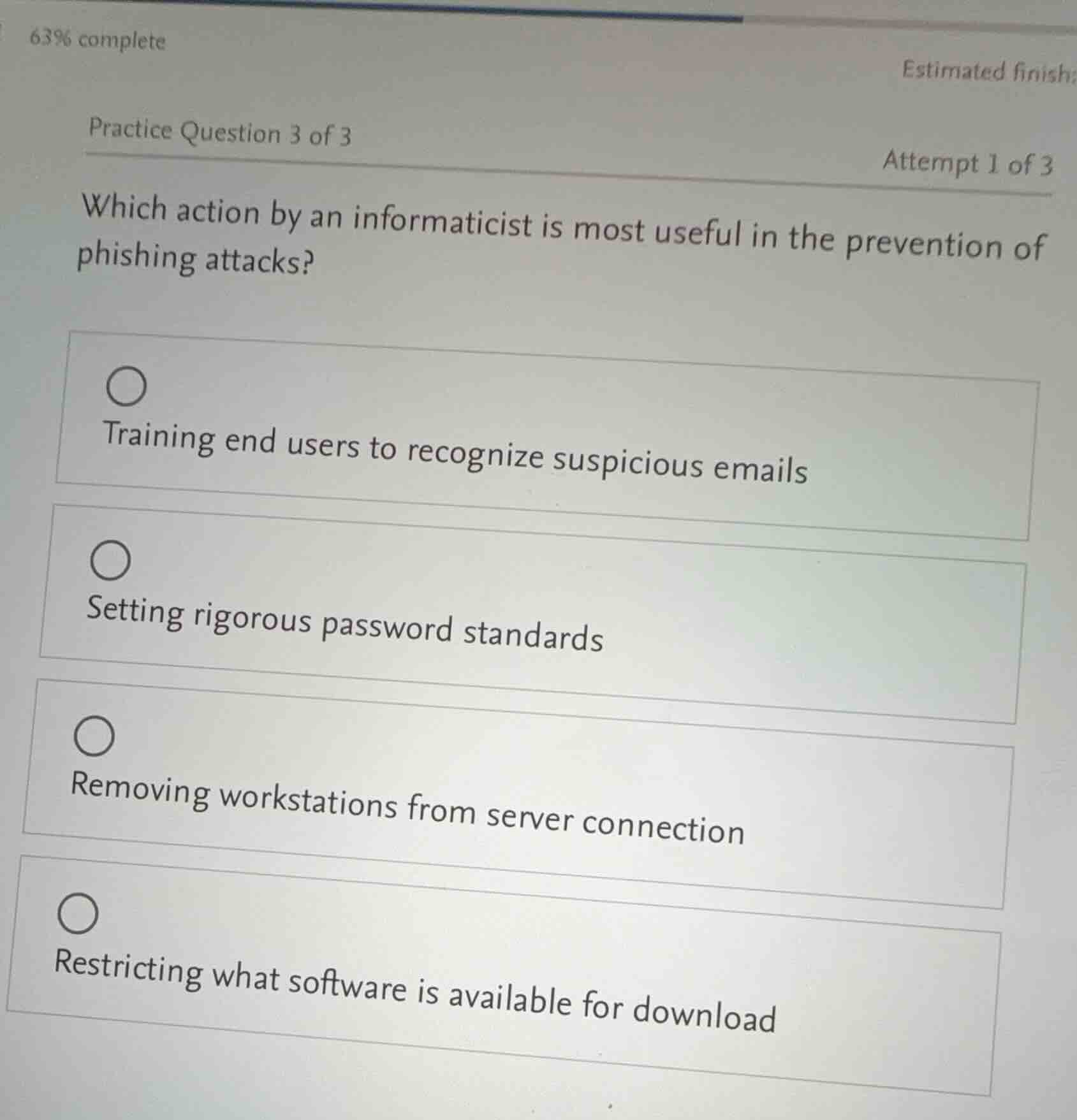
practice question 3 of 3
attempt 1 of 3
which action by an informaticist is most useful in the prevention of phishing attacks?
training end users to recognize suspicious emails
setting rigorous password standards
removing workstations from server connection
restricting what software is available for download
Phishing attacks often occur via suspicious emails tricking users. Training end - users to recognize such emails directly targets the main vector of phishing (email - based deception). Setting password standards is for password - related security, not phishing prevention. Removing workstations from server connection is not a typical phishing prevention method. Restricting software download is for malware - related issues, not phishing. So training end users to recognize suspicious emails is the most useful.
Snap & solve any problem in the app
Get step-by-step solutions on Sovi AI
Photo-based solutions with guided steps
Explore more problems and detailed explanations
A. Training end users to recognize suspicious emails