QUESTION IMAGE
Question
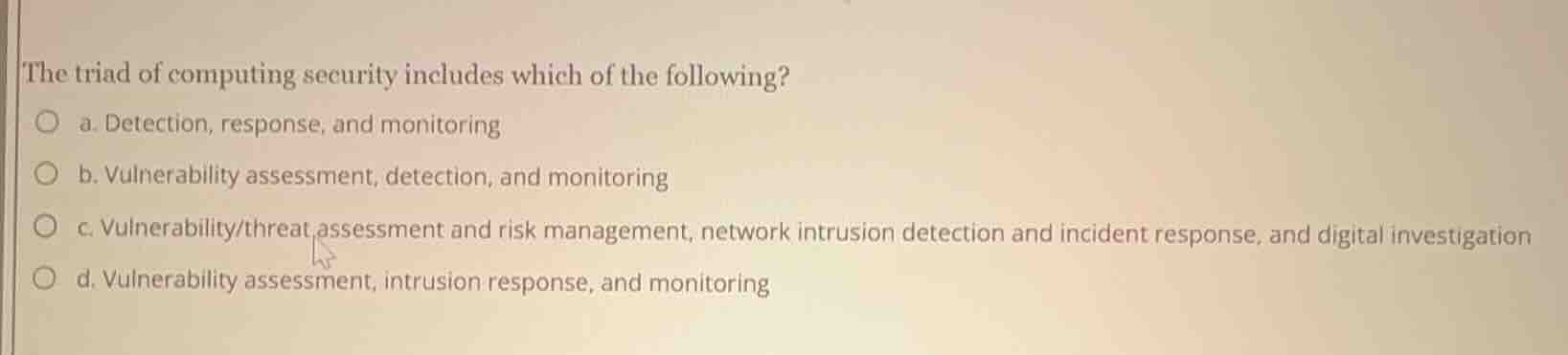
the triad of computing security includes which of the following?
a. detection, response, and monitoring
b. vulnerability assessment, detection, and monitoring
c. vulnerability/threat assessment and risk management, network intrusion detection and incident response, and digital investigation
d. vulnerability assessment, intrusion response, and monitoring
The core triad of computing security operations centers on three key functional areas: proactive risk and threat evaluation, real-time threat detection and incident response, and post-incident digital investigation to understand and mitigate future risks. The other options only cover partial or operational sub-tasks rather than the full triad.
Snap & solve any problem in the app
Get step-by-step solutions on Sovi AI
Photo-based solutions with guided steps
Explore more problems and detailed explanations
c. Vulnerability/threat assessment and risk management, network intrusion detection and incident response, and digital investigation