QUESTION IMAGE
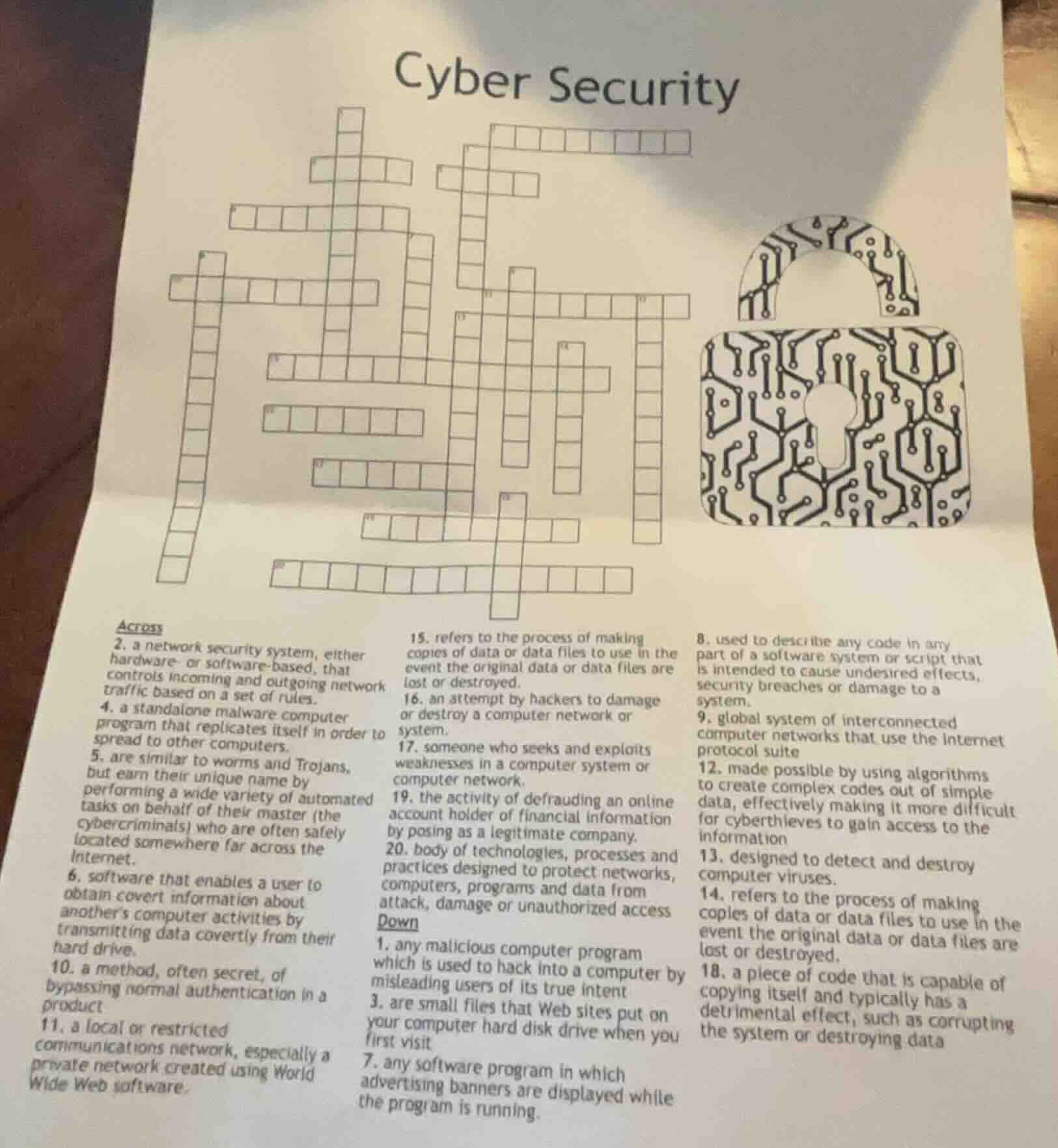
Question
cyber security
across
- a network security system, either hardware- or software-based, that controls incoming and outgoing network traffic based on a set of rules.
- a standalone malware computer program that replicates itself in order to spread to other computers.
- are similar to worms and trojans, but earn their unique name by performing a wide variety of automated tasks on behalf of their master (the cybercriminals) who are often safely located somewhere far across the internet.
- software that enables a user to obtain covert information about anothers computer activities by transmitting data covertly from their hard drive.
- a method, often secret, of bypassing normal authentication in a product
- a local or restricted communications network, especially a private network created using world wide web software.
- refers to the process of making copies of data or data files to use in the event the original data or data files are lost or destroyed.
- an attempt by hackers to damage or destroy a computer network or system.
- someone who seeks and exploits weaknesses in a computer system or computer network
- the activity of defrauding an online account holder of financial information by posing as a legitimate company.
- body of technologies, processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access
down
- any malicious computer program which is used to hack into a computer by misleading users of its true intent
- are small files that web sites put on your computer hard drive when you first visit
- any software program in which advertising banners are displayed while the program is running.
- used to describe any code in any part of a software system or script that is intended to cause undesired effects, security breaches or damage to a system.
- global system of interconnected computer networks that use the internet protocol suite
- made possible by using algorithms to create complex codes out of simple data, effectively making it more difficult for cyberthieves to gain access to the information
- designed to detect and destroy computer viruses.
- refers to the process of making copies of data or data files to use in the event the original data or data files are lost or destroyed.
- a piece of code that is capable of copying itself and typically has a detrimental effect, such as corrupting the system or destroying data
Brief Explanations
Below are the solved answers for the cybersecurity crossword, matched to each clue:
Across:
- A network traffic control system (hardware/software) → FIREWALL
- Self-replicating standalone malware → WORM
- Automated malware controlled remotely → BOT
- Software to spy on computer activity → SPYWARE
- Bypass normal authentication → EXPLOIT
- Restricted private network → INTRANET
- Data copy for loss recovery → BACKUP
- Hacker attempt to damage systems → CYBERATTACK
- Exploits system weaknesses → HACKER
- Fake company to steal financial data → PHISHING
- Protective tech/processes for systems → CYBERSECURITY
- Malicious code for system harm → MALWARE
- Global interconnected computer network → INTERNET
- Scramble data to block access → ENCRYPTION
- Detects and removes viruses → ANTIVIRUS
- Data copy for loss recovery → BACKUP
- Self-copying harmful code → VIRUS
Down:
- Malware that misleads users → TROJAN
- Small files from websites → COOKIES
- Software with advertising banners → ADWARE
Snap & solve any problem in the app
Get step-by-step solutions on Sovi AI
Photo-based solutions with guided steps
Explore more problems and detailed explanations
Across:
- FIREWALL
- WORM
- BOT
- SPYWARE
- EXPLOIT
- INTRANET
- BACKUP
- CYBERATTACK
- HACKER
- PHISHING
- CYBERSECURITY
- MALWARE
- INTERNET
- ENCRYPTION
- ANTIVIRUS
- BACKUP
- VIRUS
Down:
- TROJAN
- COOKIES
- ADWARE